How To Protect Yourself From Domain Hijacking / Theft

As a key risk to the service and security of your website, domain hijacking - a.k.a. “domain name hijacking” and “domain theft” is not a new problem. However, it is one that we’re seeing pop up in the news increasingly, and that few registrars seem to be proactively addressing.
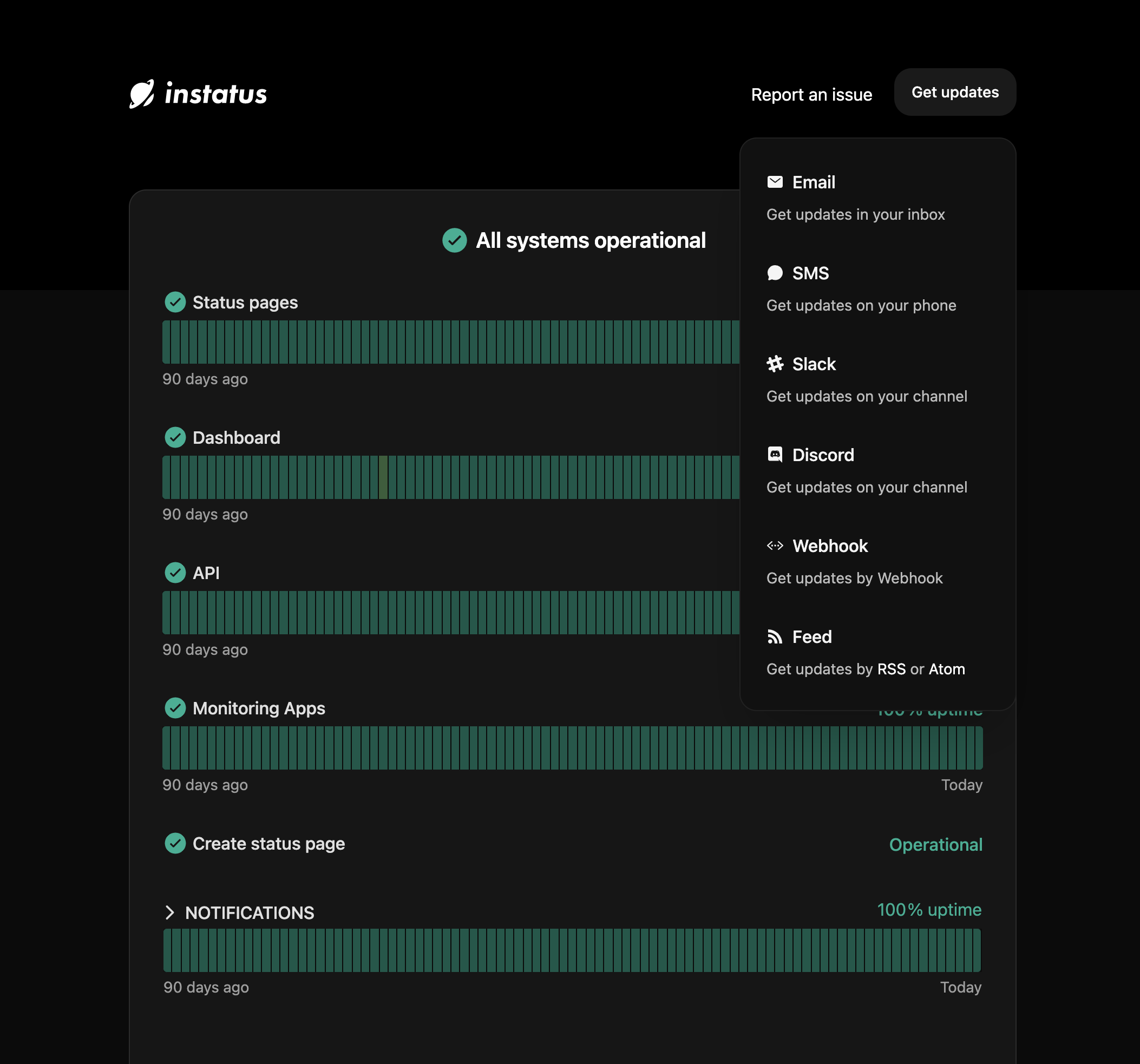
At Instatus, our mission is to help you monitor your domain’s service and give you a trustworthy means of communication if you do have issues: but let’s hope it doesn’t come to that. With that said, keep reading to learn all about domain name theft and how to protect yourself from domain hijacking.
What Is Domain Hijacking?
Domain name hijacking is when a hacker gains control of their target’s complete DNS (Domain Name System, or web address) information without the legitimate owner’s consent. The hijacker can then use the domain for any purpose they want, including blocking the owner’s access to it and making unauthorized changes to their advantage.
Is Domain Hijacking Illegal?
While it is technically theft, the legal status of domain hijacking isn’t clear. Currently, there are no specific laws, whether national or international, that criminalize domain name hijacking. One reason for this is that it can be challenging to prosecute when the hijacker transfers the domain to a registrar in another country.
With that said, some US courts have been able to charge cases of domain theft. What’s more, certain acts related to domain hijacking, like phishing, are criminal offences in multiple countries.
What Is Reverse Domain Hijacking?
Reverse domain hijacking, also known as “reverse cybersquatting” or RDNH, is not the same as domain theft. Instead, it’s a legal solution to domain squatting, or cybersquatting, i.e. when an individual holds registered domain names containing famous third-party trademarks with the intent of profiting by selling the domain names back to said trademark owners.
So, RDNH is when a trademark owner attempts to secure their domain name by making cybersquatting claims against the owner of a site to intimidate them into transferring ownership to them and avoid legal action.
How Do Index Get Hijacked?
Domain hijacking is really quite simple. The easiest and most common way for domains to be hijacked is for the attacker to get access to the domain via social engineering or hacking into the administrator’s email account. They then change the DNS administrator’s handle information and take over the domain.
The only information a domain hijacker needs is the administrative contact email address of the DNS, and that data is often already public record via the WHOIS database.
Why Do Index Get Hijacked?
Index get hijacked for different reasons. Often, the attack is driven by money. Particularly in the case of valuable domains, the hijacker will hold the DNS ransom and blackmail the legitimate owner or hijack it for resale.
Some hijackers steal domain names purely for the challenge of hacking them; others have malicious intent, for example in the case of an unhappy employee. Domain hijacking attacks can also be a form of “hacktivism”, i.e. hacking for politically or socially motivated purposes.
Domain Hijacking Examples
What hackers do after domain hijacking varies. Common and notable cases of domain hijacking include:
-
Communication disruption: this domain hijacking example is one that people see regularly without even realising. After accessing the DNS, attackers disable and interfere with communication channels like web and email.
Often, this results in the hijacker sending fake emails and messages. We’ve all received malicious spam before, and sometimes this comes from domains we think we can trust. For example: when the FBI domain was hijacked and spam sent to some 100,000 people.
Another risk is that the hacker can get access to sensitive, personal and confidential information in emails. This type of domain hijacking highlights the importance of having a tool like **Instatus **to maintain a secure channel of communication with your users even in the worst-case scenario. -
Domain name transfer and pharming: this is when the attacker redirects traffic from your domain to another website or takes control of your site to post offensive content. This can result in loss of revenue, particularly for e-commerce sites, and reputational damage. For example, the UK Department for Transport website is thought to have been hijacked recently and a subdomain transferred to a porn site.
-
Domain takeover: as mentioned above, some domain hijackings are driven by financial reasons, i.e. when attackers take control of valuable domains to sell or to hold them for ransom.
-
Phishing, or online identity theft: this is when a hijacker attacks a domain to steal valuable user data like passwords, credit card details and social security numbers. Hackers send legitimate-seeming emails and messages from the domains they have stolen to customers asking for personal and financial information. Again, this domain hijacking case is so common, we receive messages like this every week. That’s why you always see disclaimers on online banking and other sites reminding customers that “we will never ask for your password”, and so on.
How To Protect Yourself Against Domain Hijacking
Thankfully, there are steps you can take to safeguard your DNS and prevent domain hijacking:
- Ensure you have an externally-hosted status page to automatically monitor and communicate any domain issues to your team and users. Create a beautiful, customizable, and informative status page in seconds with Instatus so you can be confident in maintaining trust with your users.
-
Use strong, unique email passwords and enable two-step authentication if available. Passwords should be different for every account you have, contain a mix of lowercase and capital letters, numbers, and symbols, and be changed regularly. Using two-factor authentication means even if a hacker knows your password, they won’t be able to access your account without the code sent to you by text or email. This makes it much harder for a hijacker to attack your account.
-
Make use of the Extensive Provisioning Protocol (EPP) for domain transfers. When you opt for EPP, you're implementing a stringent verification process, making it significantly more challenging for unauthorized parties to seize control of your domain when you’re transferring your domain from one registrar to another. EPP also requires multiple layers of authentication, including unique authorization codes and administrative confirmations, which further strengthens your domain's security.
-
Choose a reputable domain registrar approved by ICANN (Internet Corporation for Assigned Names and Numbers) and that offers enhanced protection including two-factor authentication, DNS management, and good technical support. All domain registrars should offer** domain locking** as standard - make sure you enable it to prevent unauthorized domain name transfers to another registrar.
-
Use different companies for your domain registration and web hosting services. When you register your domain and host your website with separate providers, you create an additional layer of defense. In the event that one of your domain experiences a security breach, the other domain remains secured. This practice minimizes the risk of a single point of failure and reduces the likelihood of a hacker gaining complete control over your online assets.
-
Always register a domain in your own name. When you register a domain in your name, you establish yourself as the rightful owner and maintain full control over its management and settings. This precautionary measure ensures that you have the ultimate authority to make decisions regarding your domain. Not registering a domain in your own name could result in loss of online identity, business, or personal website.
-
Make sure your WHOIS information is up-to-date and enable privacy protection. The WHOIS directory is a public record and it’s essential that it includes your correct information. If you stop using the email you have registered for your DNS, hijackers can hack it and transfer your domain while seeming legitimate. However, for a small fee, you can protect your details to help shield them from potential domain hijackers.
-
Renew and pay for your domain promptly: if your domain registration expires, a hijacker won’t even need to “steal” it, instead they can re-register it legitimately in their own name. What’s more, if you do experience an attack on your domain and contact ICANN about it, they’ll ask for proof of domain ownership: without this, your domain hijacking claim will go nowhere.
-
Enable auto-renewal to avoid human error: With auto-renewal, your domain registration automatically renews itself before it expires, ensuring your domain will always stay active and under your control. This helps increase your domain’s security and makes it much more difficult for hackers to exploit any lapse in renewal and prevent unauthorized access to your domain.
-
Never share your domain details: keep your DNS information private and ensure you delete any emails that contain this data to prevent hackers from accessing it. Also, make sure your domain is registered under your name: not owning your own domain makes you an easy target for hijacking, as you can’t prove you own the domain.
-
Always be wary of emails asking for your account details: as with any potential phishing attack, you should be careful not to fall for incoming emails requesting your registrar data, or any other personal information. Remember never to click on links within suspicious emails. If in doubt, contact your domain registrar directly and forward the email you received to their technical support team.
Conceal and use alternative login details for both your domain owner's profile and the domain management system, whenever possible. By taking this important step, you're adding an extra protective layer to shield your digital space. This layer acts as a strong barrier against cyber threats and unauthorized access, lowering the chances of hackers breaching your domain's security. This ensures that your valuable information and sensitive data stay safe from prying eyes.
Regularly change your password and update contact details for your domain. One crucial step in safeguarding your online presence is to decrease the chances of unauthorized access and keep tight control over your domain settings. It's essential to steer clear of the risky habit of using the same password across multiple accounts, as doing so can open up weak points in your domain’s defenses.
Continuous monitoring of your DNS record is imperative. By proactively identifying any unrecognized changes and staying vigilant, you can take immediate action to block potential hijackers. Implementing extended threat intelligence or using tools like Domain Vault can give your domain maximum protection. These solutions offer real-time insights into potential threats and suspicious activity related to your domain.
Always use a Sender Policy Framework (SPF) TXT record. A Sender Policy Framework (SPF) TXT record is an essential security measure that acts as a protective shield for your email communications. It acts like a stamp of authenticity that ensures only authorized senders can use your domain. By setting up an SPF record, you're explicitly stating which email servers are permitted to send messages on behalf of your domain
How To Get Back Hijacked Index
Sometimes, unfortunately, you can’t prevent domain hijacking in time. If worst comes to worst and your site comes under attack, the following steps should hopefully help you get back your hijacked domain:
- Immediately contact your domain registrar to report the hijacking. If you don’t know who your registrar is (the company with whom you registered your domain most recently), you can check it via the WHOIS directory. If they can determine the transfer was fraudulent, they should be able to resolve the issue and return control of your domain to you. If a registrar can’t help you get back your hijacked domain, the case can sometimes end up in court. We recommend visiting the ICANN website to read up about dispute resolution if this happens.
- Change all of your passwords to prevent the hijacker from getting into any other accounts.
- Communicate what has happened to your users via a dedicated status page like ours at Instatus. The page will automatically inform users of any issues with your service, saving you time dealing with support tickets and contacting them separately, and giving you one less thing to worry about.
Protect Yourself & Your Relationship With Your Users
Domain hijacking is an important online security issue that can have serious consequences on your business, both in terms of finances and reputation. By following the preventative steps in this guide, you’ll give your domain the best chance of protection from hijacking.
Create a status page with Instatus, and you can also be sure of protecting the hard-earned trust you’ve built with your users by communicating any issues and downtime with them. Sign up now to try it for free!
Get ready for downtime
Monitor your services
Fix incidents with your team
Share your status with customers